The ultimate risk prioritization blueprint for 2025 — now with actionable hunting tips, dev fixes, and emerging threats.

Table of Contents
Open Table of Contents
Overview
Release Date: 6 November 2025
Status: Release Candidate 1 (RC1)
Data Source: Over 2.8 million applications + global community survey
CWEs Mapped: 248 across 10 categories (avg. 25 per category, max 40)
Why This Matters
For bug bounty hunters, pentesters, security engineers, and developers, the OWASP Top 10:2025 is your attack & defense roadmap. It reveals:
- What attackers exploit most
- Where automated tools fail
- How to chain flaws for max impact
- How to build secure by design
Full Top 10:2025 – Ranked with Actionable Insights
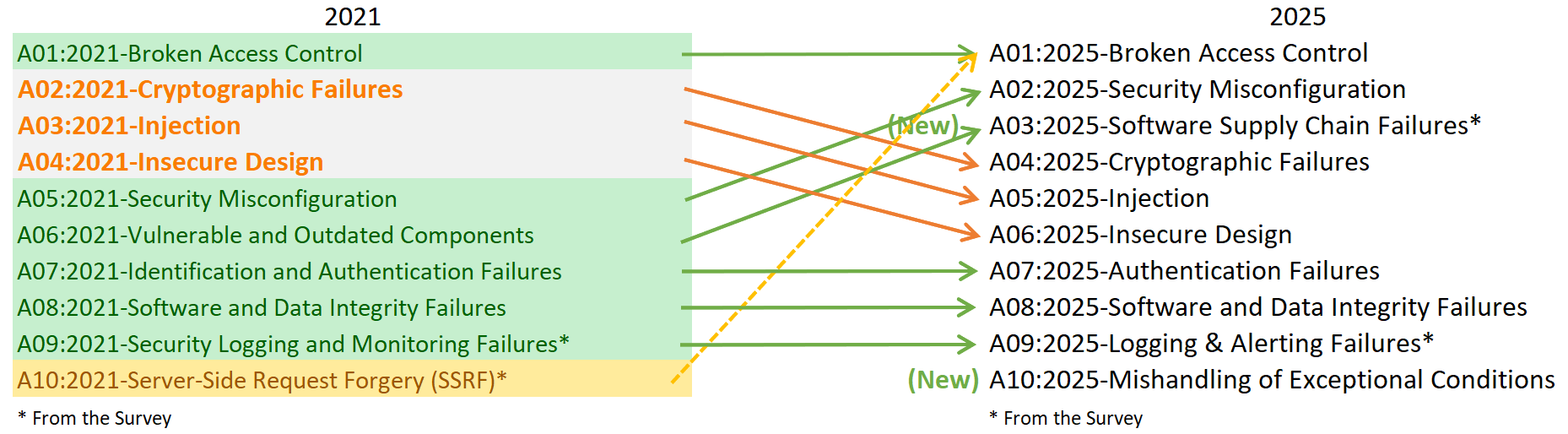
| Rank | Category | 2021 → 2025 | Prevalence* | CWEs | Bug Bounty / Pentest Tips | Dev Remediation Focus |
|---|---|---|---|---|---|---|
| A01 | Broken Access Control | #1 → #1 | 3.73% | 40 | IDOR, vertical/horizontal escalation, SSRF (merged), forced browsing, CORS misconfig, JWT none, path traversal, mass assignment | RBAC/ABAC, indirect refs, server-side validation, zero-trust authz, ZAP/Burp scans |
| A02 | Security Misconfiguration | #5 → #2 | 3.00% | 16 | Debug pages, default creds, verbose errors, public S3, missing headers (CSP/HSTS), debug in CI/CD | IaC scanning, secure defaults, auto-hardening (AWS Config), remove unnecessary services |
| A03 | Software Supply Chain Failures | NEW | Low in data | 5 | Typosquatting, CI/CD compromise, unsigned binaries, SBOM tampering, pipeline secrets | SBOMs, in-toto, artifact signing, dependency locking, Dependabot/SNYK alerts |
| A04 | Cryptographic Failures | #2 → #4 | 3.80% | 32 | Weak RNG, hardcoded keys, MD5/SHA1, ECB, no TLS, secrets in logs/memory | libsodium, TLS 1.3, key rotation, HSM, avoid custom crypto |
| A05 | Injection | #3 → #5 | High CVEs | 38 | SQLi, NoSQLi, XSS, LDAP, XXE, SSTI, Log Injection | Parameterized queries, safe ORM, output encoding, strict CSP, allowlisting |
| A06 | Insecure Design | #4 → #6** | Improving | Varies | No rate limits, weak MFA, logic bypass, insecure defaults | STRIDE modeling, secure patterns, abuse cases, privacy-by-design |
| A07 | Authentication Failures | #7 → #7 | Stable | 36 | Brute force, weak recovery, session fixation, JWT weak signing | MFA, WebAuthn, secure sessions, breach monitoring |
| A08 | Software or Data Integrity Failures | #8 → #8 | Stable | Varies | Insecure deserialization, untrusted exec, missing signatures | Safe deserializers (JSON), input validation, code signing, hash pinning |
| A09 | Logging & Alerting Failures | #9 → #9 | Low in data | 5 | No logs, PII leaks, no alerts, log injection | Log auth events, SIEM, anomaly alerts (e.g., 100 failed logins) |
| A10 | Mishandling of Exceptional Conditions | NEW | N/A | 24 | Crash on null, fail-open, stack traces, infinite loops, DoS via exceptions | Fail securely, circuit breakers, fuzzing, crash monitoring |
*Prevalence = % of apps with ≥1 instance of mapped CWEs (frequency ignored to avoid tool bias)
Methodology Deep Dive
| Aspect | Details |
|---|---|
| Data | 589 CWEs from 2.8M+ apps (2021–2025) |
| Prevalence | % apps with ≥1 CWE – no frequency bias |
| Exploit & Impact | Weighted CVSSv2 + CVSSv3 from ~220K CVEs |
| Top 8 | Data-driven |
| Top 2 | Community survey promoted (emerging risks) |
| Focus | Root cause > symptoms for better fixes |
CVSS v4 Note: Not used due to missing Exploit/Impact split. Future support planned.
Pro Tips for Bug Hunters & Pentesters
1. A03: Supply Chain – High Reward, Low Noise
- Scanners miss malicious packages & CI/CD attacks
- Inspect:
package.json,pom.xml,requirements.txt- GitHub Actions / Jenkins
- SBOMs
- Tools: Dependency-Check, SNYK, OSS Index
- Report: typosquatting, protestware, backdoors
2. A10: Exceptional Conditions – The New Frontier
- Fuzz edge cases: null, empty, huge, special chars
- Trigger exceptions → stack traces?
- Hunt fail-open logic: “DB down → allow all”
- Tools: Burp Intruder, ffuf, nuclei
3. Chain for Impact
A01 (IDOR) → A04 (decrypt) → A09 (no log) = Silent Exfil→ Higher severity, bigger bounty
For Developers & SecDevOps
Automate Early
| Risk | Tools |
|---|---|
| A01–A05 | Semgrep, CodeQL, SonarQube |
| A03 | Dependabot, Trivy, Grype |
| A09 | ELK + Falco, Splunk, Datadog |
| Design | ThreatPlaybook, PyTM |
Secure SDLC Checklist
- Threat model every feature
- Generate SBOM in CI
- Run SAST + DAST
- Scan secrets (GitGuardian)
- Enable RASP/runtime monitoring
Next Steps
- Read the full RC1: OWASP Top 10:2025 RC1
“We focus on root cause over symptoms — because fixing the disease beats treating the fever.”
Stay sharp. Ship secure. Hunt smart.